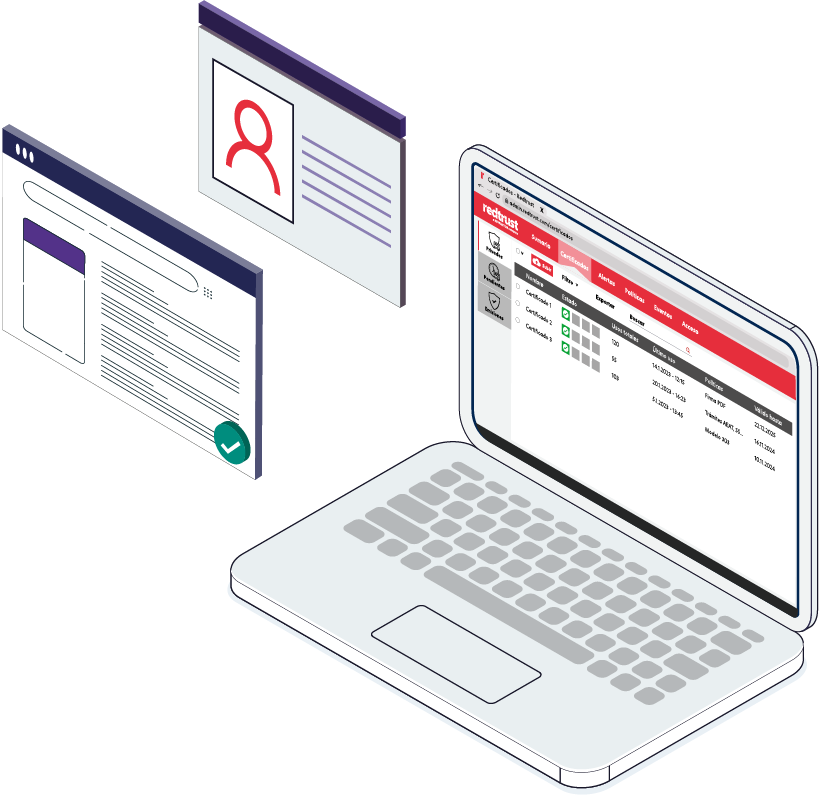
Easy management of digital identities
Create usage policies, centralized certificate lifecycles, and get detailed audits to maintain control and security of your certificates.
Total control and security when carrying out online procedures with digital certificate
⇒ Ensure the authentication of your employees when carrying out telematic procedures with the different Public Administration bodies.
⇒ Control for which specific procedures and in which electronic offices, such as the Tax Agency, users can be authenticated with the digital certificate.
One solution for all your Digital Identity Management
Redtrust is a patented solution that answers all of the challenges presented by the day-to-day management of digital certificates in a simple and transparent manner.
![]()
Secure Identity Storage
Digital Identities are stored in a single controlled and secure repository so they do not travel across networks or devices.
With centralized digital certificates your employees can prove their identity from anywhere and at any time.
![]()
Detailed audit and traceability
Organizations have complete control and usage traceability such as the Who, How, When, Where of all the certificate operations.
![]()
Theft and Data breaches
With the certificate not residing on the workstation this eliminates the risk of theft, also the certificate credentials can be revoked or canceled in the central storage location at any time.
![]()
Usage policies
Through an easy and efficient system of policies, Redtrust allows you to restrict users’ access to a certain number of certificates, limit operations with certificates to a specific number of pages or applications.
Additional two-factor authentication and time time control configuration are available to create an added layer of security.
![]()
Centralized life cycle management
Instead of manually applying actions to all individual workstations, it is possible to use the central administration site to send centralized actions to all workstations for which the actions may apply.
![]()
Secure, transparent and compatible integration
Redtrust’s complete cycle management is performed from a web browser and does not require any complicated client-side integration, making the user-experience totally transparent and unchanged while allowing the use of other local certificates that could be found on the workstation.
Integration with the corporate credential system. Easy event logging on remote systems.
How Redtrust solves digital identity management
Former manual Digital Identity Management
Redtrust
Storage
A certificate copy is needed for as many machines and/or users use them. No control exists over the copies that can be made.
Certificates are found in a single secure repository, and not on the individual workstations.
![]()
Transport
The installation of a certificate requires sending it via a physical or electronic method, which exposes the certificate to theft and data breaches.
There is no transportation because the certificate does not reside on the machine where it is used.
![]()
Implementation
Complex process that requires time and technical or helpdesk action.
Granting a user the ability to use a certificate requires only one click.
![]()
Usage
It is not possible to establish policies of use nor is it possible to guarantee identity or authenticate a user.
Allows you to establish policies for total access control. User authentication is guaranteed.
![]()
Monitoring
It is not possible to audit use of the certificates.
Full record of all user and certificate actions.
![]()
Recovery
In case of data or physical loss of an information system, a new copy of the certificate is needed.
The certificate is centralized and not found on a user’s machine.
![]()
Expiration
In general, we know about a certificate’s expiration after it has already occurred.
System auditing informs us of the expiration in advance.
Destruction
There is no way to guarantee the destruction of a certificate without a technical action to guarantee it.
The certificate is destroyed in the central storage location and in compliance with Federal Information Processing Standards (FIPS).
Ensuring secure digital identity in your company
Discover why Redtrust is an essential tool for the management, control and security of your digital certificates
Among the services that we offer, our organisation is authorised to issue digital certificates, either for individuals or legal entities. We currently manage a volume of more than 600 certificates from our clients and the Redtrust tool is indispensable to us in order to maintain control and security over them.”

